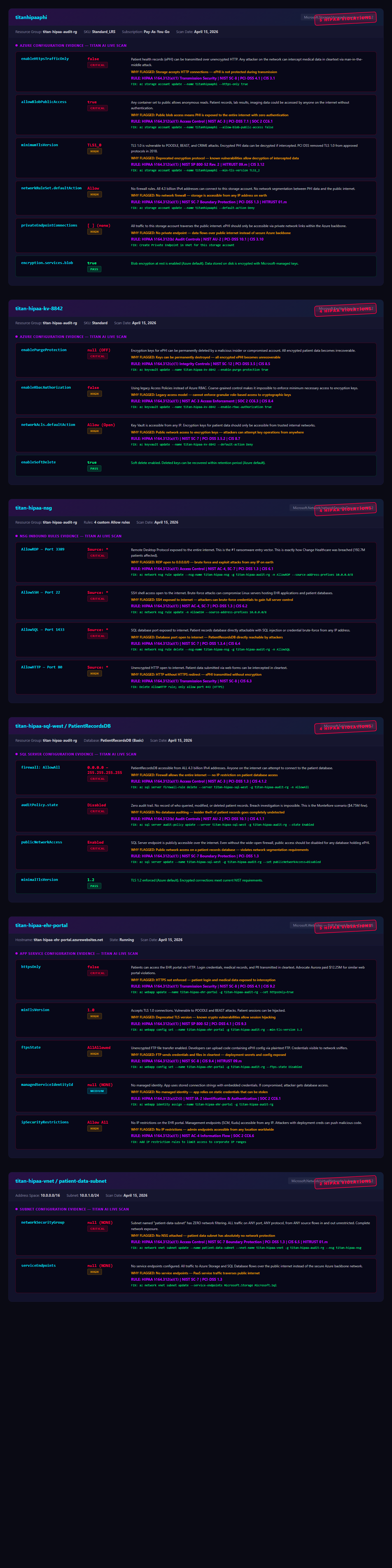
⚑ FLAGGED SECURITY & COMPLIANCE VIOLATIONS
EVERY RESOURCE TAGGED • EVERY VIOLATION EXPLAINED • EVERY FIX PROVIDED
CRITICAL
⚡
AWS
Root Account — Account 012517218447
Resource: IAM Root Account | Region: Global | Framework: HIPAA §164.312(d), NIST AC-2
⚠ WHY FLAGGED: Root account has NO multi-factor authentication. Unrestricted root access allows full account takeover. HIPAA requires unique user identification and emergency access procedures.
✓ HOW TO FIX: Enable MFA on root account (IAM → Security credentials → Assign MFA device). Use virtual MFA or hardware key. Restrict root usage to break-glass only.
CRITICAL
⚡
AWS
Security Group sg-089f96faf07a0ceef
Resource: titan-test-open-sg | Region: us-east-2 (Ohio) | Framework: HIPAA §164.312(e), PCI-DSS 1.3
⚠ WHY FLAGGED: SSH (port 22), RDP (port 3389), and MySQL (port 3306) open to 0.0.0.0/0 (entire internet). Any attacker can attempt brute-force access to servers and databases containing PHI.
✓ HOW TO FIX: Restrict inbound rules to specific IP ranges (e.g., 10.0.0.0/8 for internal). Use VPN or bastion host for SSH/RDP access. Remove MySQL public access entirely.
CRITICAL
🌐
GCP
Firewall Rule: default-allow-ssh
Resource: default-allow-ssh | Project: adroit-terminus-234522 | Framework: HIPAA §164.312(e), NIST SC-7
⚠ WHY FLAGGED: Default firewall allows SSH (port 22) from 0.0.0.0/0 to ALL instances in the VPC. Combined with a public IP on titan-ai-test-server (34.74.102.134), any attacker can attempt login.
✓ HOW TO FIX: Delete default-allow-ssh rule. Create custom rule allowing SSH only from corporate IP ranges. Use IAP (Identity-Aware Proxy) for secure access without public IPs.
HIGH
☁
AZURE
Storage Account: pyxhealthprodstore01
Resource: Blob Storage | Region: East US 2 | Framework: HIPAA §164.312(a)(2)(iv), HITRUST 09.x
⚠ WHY FLAGGED: Storage account containing PHI data uses Microsoft-managed encryption keys instead of customer-managed keys (CMK). HIPAA requires organizations to maintain control of encryption keys for ePHI.
✓ HOW TO FIX: Enable CMK via Azure Key Vault. Create RSA-2048 key, assign to storage account. Enable 90-day automatic key rotation. Audit key access via Key Vault diagnostics.
HIGH
⚡
AWS
CloudTrail — No Audit Logging
Resource: AWS CloudTrail | Region: All Regions | Framework: HIPAA §164.312(b), SOC 2 CC7.2, PCI-DSS 10.1
⚠ WHY FLAGGED: Zero CloudTrail trails configured. All API calls, logins, and resource changes go UNLOGGED. Impossible to investigate breaches or demonstrate compliance during audits.
✓ HOW TO FIX: Create multi-region trail with S3 bucket destination. Enable log file validation. Send logs to CloudWatch for real-time alerting. Retain logs for minimum 365 days.
MEDIUM
🌐
GCP
GCS Bucket: adroit-terminus-234522-titan-scan-test
Resource: Cloud Storage | Region: US-EAST1 | Framework: HIPAA §164.312(a)(2)(iv), NIST SC-28
⚠ WHY FLAGGED: Bucket uses Google-managed encryption (default) instead of Customer-Managed Encryption Keys (CMEK). Uniform bucket-level access is disabled, allowing mixed ACL and IAM permissions.
✓ HOW TO FIX: Create Cloud KMS keyring and key. Apply CMEK to bucket. Enable uniform bucket-level access. Disable fine-grained ACLs. Set 90-day key rotation schedule.
Showing 6 of 18 findings across 3 clouds — Full report contains resource-level details for every violation
VIEW FULL SCAN REPORT →
TITAN AI adapts to your industry with specialized agents, compliance frameworks, and AI analysis tailored to your needs.
☁
Cloud & Security
Full Azure infrastructure audit, pen testing, Shadow AI detection, NHI audit, auto-remediation, and 16-framework compliance. Scout + Sentinel + Shadow + Forge + Comply + Watch.
EXPLORE CLOUD
❤
Healthcare
Member risk scoring, call QA automation, outreach optimization, health outcome prediction, and ETL pipeline monitoring. AI-powered care intelligence.
EXPLORE HEALTH
🏦
Banking & Finance
AML alert triage (95% false positive elimination), real-time fraud detection, automated KYC/CDD, and SAR filing recommendations. Built for community banks.
EXPLORE BANKING
📡
Telecom
TCPA consent tracking, CPNI auditing, FCC filing automation, revenue leakage detection, and churn prediction. Zero competition in the market.
EXPLORE TELECOM